Decentralized finance has unlocked extraordinary financial opportunities, but it has also introduced risks that traditional banking never faced. In 2024 alone, DeFi exploits drained over $1.7 billion from protocols, and many of those losses traced back to unaudited or poorly audited smart contracts. If you are putting money into any DeFi protocol, understanding smart contract audits is no longer optional — it is essential for protecting your assets.
This guide walks you through everything you need to know about smart contract audits: why they matter, who performs them, how to read an audit report, what red flags to watch for, and which free tools you can use to verify contracts yourself.
What Is a Smart Contract Audit?
A smart contract audit is a systematic review of a blockchain protocol’s source code by independent security experts. Auditors examine the logic, architecture, and potential vulnerabilities of the code before (or sometimes after) it is deployed on-chain. The goal is straightforward: find bugs, logic errors, and security flaws that attackers could exploit to steal funds or manipulate the protocol.
Think of it like a building inspection before you move in. The inspector does not guarantee the building will never have problems, but they identify structural weaknesses, code violations, and safety hazards that need fixing. A smart contract audit works the same way for DeFi protocols.
Why Smart Contract Audits Matter for DeFi Security
Smart contracts are immutable once deployed. Unlike traditional software that can be patched with a quick update, a deployed smart contract on Ethereum or Solana lives on the blockchain permanently. If a vulnerability exists in the code, attackers can exploit it repeatedly until the funds are drained.
Here is why audits are critical for DeFi security:
- Rug pull protection: Auditors can identify hidden mint functions, backdoor admin keys, or mechanisms that allow developers to drain liquidity pools.
- Logic error detection: Even well-intentioned developers make mistakes. Audits catch flawed reward calculations, incorrect access controls, and reentrancy vulnerabilities.
- Investor confidence: Protocols with reputable audits attract more total value locked (TVL) because users trust that the code has been professionally reviewed.
- Regulatory alignment: As governments introduce DeFi regulations, having audit documentation demonstrates due diligence and compliance readiness.
Top Smart Contract Audit Firms
Not all audit firms are created equal. The reputation, methodology, and track record of the auditor matter as much as the audit itself. Here are the most respected firms in the industry:
CertiK
CertiK is one of the largest blockchain security firms, having audited over 4,700 projects. They use a combination of formal verification (mathematical proof of code correctness) and manual review. CertiK also provides a public Skynet security score for audited projects, making it easy for investors to check a protocol’s security rating. However, some critics note that CertiK’s high volume of audits can sometimes result in less depth per engagement.
Trail of Bits
Trail of Bits is a boutique security firm known for deep, research-driven audits. They work with major DeFi protocols and have published significant open-source security tools, including Slither (a static analysis framework for Solidity). Their audits tend to be extremely thorough, and they are often the choice for high-value protocols that demand the highest level of scrutiny. Trail of Bits is selective about the projects they take on.
OpenZeppelin
OpenZeppelin is arguably the most influential name in smart contract security. Their open-source contract libraries (OpenZeppelin Contracts) are used by the majority of ERC-20 and ERC-721 token implementations. Their audit team has reviewed protocols managing billions in TVL, including Compound, Aave, and the Ethereum Foundation. An OpenZeppelin audit carries significant weight in the industry.
Spearbit
Spearbit takes a decentralized approach to auditing. They maintain a network of elite independent security researchers who collaborate on audits. This model allows them to assemble specialized teams for each engagement, matching the right expertise to the protocol being audited. Spearbit has gained recognition for auditing complex DeFi protocols and novel cryptographic implementations.
Audit Firm Comparison Table
| Firm | Methodology | Notable Clients | Public Reports | Best For |
|---|---|---|---|---|
| CertiK | Formal verification + manual review | PancakeSwap, Aave, Polygon | Yes (Skynet) | Broad coverage, public scoring |
| Trail of Bits | Deep manual + custom tooling | MakerDAO, Uniswap, Yearn | Yes (GitHub) | Complex protocols, research depth |
| OpenZeppelin | Manual review + formal methods | Compound, Aave, Ethereum Foundation | Yes (blog) | Battle-tested expertise, token standards |
| Spearbit | Decentralized researcher network | Various DeFi blue chips | Selective | Specialized expertise matching |
How to Read a Smart Contract Audit Report
Knowing how to check a smart contract audit report is a skill every DeFi investor should develop. Audit reports follow a fairly standard structure, and once you know what to look for, you can evaluate them in minutes.
Key Sections of an Audit Report
- Executive Summary: A high-level overview of the audit scope, methodology, and overall findings. This tells you what was reviewed and whether the auditors found critical issues.
- Scope and Objectives: Lists the specific contracts and commit hashes that were audited. If the deployed contract uses a different commit hash than the audited version, the audit may not cover the actual deployed code.
- Findings by Severity: Issues are categorized as Critical, High, Medium, Low, or Informational. Critical and High findings indicate potentially exploitable vulnerabilities.
- Remediation Status: Shows whether the development team fixed the reported issues. Look for “Resolved” or “Acknowledged” labels. “Acknowledged” means the team is aware but chose not to fix it — a potential red flag depending on the severity.
- Appendices: Technical details, code snippets, and proof-of-concept exploits for the identified vulnerabilities.
What to Focus On
When reading an audit, pay closest attention to the number of Critical and High findings and whether they were resolved. A protocol that launched with unresolved Critical findings is a major warning sign. Also check the date — an audit from two years ago may not cover recent code changes or added features.
Red Flags Checklist: Signs a DeFi Protocol May Not Be Safe
Even with audits, you need to stay vigilant. Use this checklist to evaluate any DeFi protocol before depositing funds:
- No audit at all: If a protocol handling significant funds has never been audited, treat it as high risk. This is the most basic form of rug pull protection — simply avoiding unaudited protocols.
- Audit by an unknown firm: Some projects commission audits from obscure firms that rubber-stamp code without thorough review. Stick to recognized audit firms.
- Unverified source code: If the contract source code is not verified on Etherscan or the relevant block explorer, you cannot confirm what the code actually does.
- Proxy contracts with no timelock: Upgradeable proxy contracts allow developers to change the logic at any time. Without a timelock (a mandatory delay before changes take effect), the team could swap the code and drain funds instantly.
- Single-owner admin keys: If one wallet address controls all admin functions (pausing, minting, upgrading), the protocol has a single point of failure.
- Unlocked liquidity: If the team’s liquidity provider tokens are not locked or vested, they can pull liquidity at any time — the classic rug pull scenario.
- No multisig governance: Reputable protocols use multisig wallets (requiring multiple signatures) for treasury and admin operations. A single externally owned account (EOA) controlling everything is dangerous.
- Forked code with modifications: Many rug pulls use forked code from legitimate protocols with small, malicious modifications. Check if the code matches a known, audited codebase.
Tools to Verify Smart Contracts Yourself
You do not need to be a developer to perform basic due diligence on smart contracts. Several free tools can help you check smart contracts and evaluate DeFi protocol safety.
Etherscan (and Other Block Explorers)
Etherscan is the primary tool for verifying smart contracts on Ethereum. Navigate to the contract address and check the “Contract” tab. Look for:
- Verified source code: A green checkmark indicates the source code has been verified and matches the deployed bytecode.
- Read/Write functions: Browse the contract’s public functions to understand what actions are possible (minting, pausing, owner-only functions).
- Transaction history: Review recent transactions for unusual patterns, large withdrawals, or suspicious admin calls.
- Token holder distribution: Check if a few wallets hold a disproportionate share of the token supply.
For other chains, use BscScan (BNB Chain), Arbiscan (Arbitrum), Polygonscan (Polygon), or Solscan (Solana).
DeFi Llama
DeFi Llama is the go-to dashboard for tracking total value locked across DeFi protocols. Use it to:
- Monitor TVL trends: A sudden, sharp decline in TVL can indicate users fleeing a compromised protocol.
- Compare protocols: See how a protocol’s TVL stacks up against competitors in the same category.
- Check audit status: DeFi Llama lists whether protocols have been audited and links to the audit reports.
- Track chain exposure: Understand which blockchains a protocol operates on and the associated risks.
RugDoc
RugDoc specializes in evaluating yield farming and DeFi projects for rug pull risk. Their reviews provide a risk rating system that categorizes projects from low risk to high risk. RugDoc’s community-driven approach means they cover many smaller, newer projects that larger audit firms have not yet reviewed. While not a substitute for a full audit, RugDoc’s risk assessments offer a quick first-pass evaluation.
Additional Verification Tools
- Token Sniffer: Automated smart contract analysis that checks for common scam patterns, honeypot mechanisms, and suspicious code.
- De.Fi Scanner: Provides automated security scores for DeFi protocols, including contract analysis and permission checks.
- Tenderly: Allows you to simulate transactions and trace contract execution, which is invaluable for understanding how a contract actually behaves.
A Step-by-Step Process for Evaluating DeFi Protocol Safety
Combining audit reports with your own research creates the strongest defense against DeFi exploits. Follow this process before committing funds to any protocol:
- Check for audits: Visit the protocol’s website or documentation. Look for links to audit reports from reputable firms.
- Read the audit report: Focus on Critical and High findings. Verify they were resolved before deployment.
- Verify the contract on Etherscan: Confirm the deployed contract matches the audited code by comparing commit hashes or contract versions.
- Review DeFi Llama data: Check TVL stability, growth trends, and whether the protocol appears on DeFi Llama’s listings.
- Run a RugDoc or Token Sniffer scan: Get a quick automated risk assessment.
- Check the team: Anonymous teams are not automatically bad, but known, doxxed teams with track records provide accountability.
- Examine governance: Verify that admin functions use multisig wallets and timelocks. Check if governance proposals and votes are public.
- Start small: Even after thorough research, limit your initial deposit. Increase exposure only as the protocol proves its reliability over time.
Limitations of Smart Contract Audits
It is important to understand that audits are not guarantees of safety. Several high-profile protocols were exploited despite having audits from top firms. Here is why:
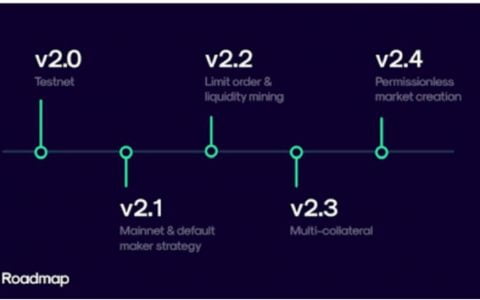
- Audits are snapshots: They cover the code at a specific point in time. Post-audit changes, upgrades, or new integrations can introduce vulnerabilities.
- Composability risk: DeFi protocols interact with each other. An audit of Protocol A does not account for how Protocol A behaves when combined with Protocol B.
- Economic exploits: Many DeFi attacks involve economic manipulation (flash loans, oracle manipulation) rather than code bugs. Not all audits cover economic attack vectors.
- Human error: Auditors are human. They can miss subtle bugs, especially in complex codebases with tens of thousands of lines.
This does not mean audits are useless — far from it. An audited protocol is significantly safer than an unaudited one. But audits should be one layer in your overall risk management strategy, not the only one.
Frequently Asked Questions
How much does a smart contract audit cost?
Costs vary widely based on the complexity of the code and the reputation of the audit firm. Simple token contracts may cost $5,000 to $15,000, while complex DeFi protocols can cost $50,000 to $500,000 or more. Trail of Bits and OpenZeppelin typically charge at the higher end, while newer firms may offer more competitive rates.
Does an audit guarantee a protocol is safe?
No. An audit significantly reduces risk by identifying known vulnerability patterns, but it cannot guarantee absolute safety. New attack vectors emerge regularly, and post-audit code changes can introduce new vulnerabilities. Always combine audit verification with your own due diligence.
Can I check if a smart contract has been audited?
Yes. Check the protocol’s official website and documentation for audit reports. You can also search DeFi Llama, DeFi Safety, and the audit firm’s public report repositories. CertiK’s Skynet dashboard and OpenZeppelin’s blog both publish completed audit reports.
What is the difference between a smart contract audit and a bug bounty?
An audit is a proactive, structured review conducted before or shortly after deployment. A bug bounty is an ongoing program that rewards independent researchers for finding vulnerabilities after deployment. The best protocols use both: audits for initial security validation and bug bounties for continuous monitoring.
Should I avoid all unaudited DeFi protocols?
Not necessarily, but you should treat them as high-risk investments. If you choose to interact with unaudited protocols, only use funds you can afford to lose entirely, and limit your exposure. Many early-stage protocols eventually get audited as they grow, but the risk window before an audit is significant.
Final Thoughts
Smart contract audits are the frontline defense in DeFi security, but they work best when combined with your own research and risk management practices. By learning how to read audit reports, recognizing red flags, and using free verification tools like Etherscan, DeFi Llama, and RugDoc, you can make significantly more informed decisions about where to put your money.
The DeFi ecosystem rewards those who do their homework. Every minute you spend verifying a protocol’s security is a minute spent protecting your capital from the next exploit. Stay skeptical, verify everything, and never invest more than you can afford to lose.
内容搜集自网络,整理者:BTCover,如若侵权请联系站长,会尽快删除。