Every transaction on Ethereum is public. Every wallet balance, every token swap, every NFT purchase, every DeFi position is recorded on a ledger that anyone on Earth can inspect with a block explorer. For a technology that was supposed to empower individuals, that level of exposure creates serious problems. Employers can screen job applicants by their on-chain activity. Merchants can price-discriminate based on a customer’s wallet balance. Attackers can identify high-value targets for phishing, social engineering, or even physical threats.
The Ethereum Foundation has decided that this default transparency is no longer acceptable. In early 2026, the Foundation formally announced the creation of a 47-expert Privacy Cluster — a dedicated working group tasked with designing, building, and deploying privacy infrastructure across every layer of the Ethereum stack. The initiative represents the largest coordinated privacy effort in Ethereum’s history, and its implications extend far beyond a single blockchain.
This article examines why privacy matters in crypto, what the Privacy Cluster is actually building, the technologies involved, how Ethereum’s approach compares to privacy-focused chains like Zcash and Canton, and what compliant privacy looks like in a world of increasing regulatory scrutiny.
Why Privacy Matters in Crypto
The case for blockchain privacy is not about hiding criminal activity. It is about basic financial dignity. In the traditional financial system, your bank balance is private. Your credit card transactions are not broadcast to the world. Your salary is not visible to anyone who knows your name. These protections exist because financial privacy is a prerequisite for personal security, commercial competitiveness, and individual autonomy.
On Ethereum today, none of these protections exist by default. A simple Ethereum Name Service (ENS) lookup can tie a real-world identity to a wallet address, and from there, the entire financial history of that individual is exposed. Businesses that use Ethereum for payroll, treasury management, or vendor payments reveal their entire financial operations to competitors. DeFi traders broadcast their positions to front-runners who extract value through sandwich attacks and other forms of maximal extractable value (MEV).
The problem has grown more acute as Ethereum adoption has expanded. With institutional players, governments, and mainstream users entering the ecosystem, the demand for private transactions on crypto networks is no longer a niche concern. It is an infrastructure requirement.
Current Ethereum Privacy Limitations
Ethereum was not designed with privacy in mind. The core protocol treats transparency as a feature, not a bug. Every state change is publicly verifiable, which is essential for the network’s security model but devastating for user privacy. Several specific limitations define the current landscape:
- Transparent account balances: Every address’s ETH and token balances are publicly visible at all times.
- Linkable transaction graphs: Blockchain analytics firms like Chainalysis and Elliptic can trace the flow of funds across addresses with high accuracy, building comprehensive profiles of user behavior.
- Public smart contract interactions: Every call to a DeFi protocol, including the parameters and amounts, is visible in the transaction data and in the mempool before the transaction is even confirmed.
- MEV exposure: The public mempool allows searchers to observe pending transactions and front-run or sandwich them for profit, costing users billions of dollars per year.
- Metadata leakage: Even when users attempt to obscure their activity through multiple wallets, IP address correlation, timing analysis, and gas payment patterns can often re-link their transactions.
Existing privacy tools on Ethereum, most notably Tornado Cash, have demonstrated both the technical feasibility and the regulatory risk of on-chain privacy. Tornado Cash’s OFAC sanctions in 2022, and the subsequent legal battles over the protocol’s smart contracts and developers, created a chilling effect that slowed privacy innovation on Ethereum for nearly three years. The Privacy Cluster represents the Foundation’s effort to restart that work on a more sustainable footing.
The Privacy Cluster Initiative
The Ethereum Foundation’s Privacy Cluster is not a single project. It is a cross-functional working group that brings together 47 researchers, cryptographers, protocol engineers, and policy experts to coordinate privacy improvements across the entire Ethereum ecosystem. The cluster operates under a simple mandate: make privacy the default on Ethereum, not the exception.
The group is organized into several workstreams, each targeting a different layer of the privacy problem:
- Protocol-layer privacy: Changes to the Ethereum core protocol that enable private state transitions, confidential transactions, and encrypted data storage on-chain.
- Application-layer tooling: SDKs, libraries, and reference implementations that make it easy for dApp developers to integrate privacy features without deep cryptographic expertise.
- Network-layer privacy: Solutions to prevent metadata leakage at the networking level, including encrypted peer-to-peer communication and private transaction propagation.
- Compliance frameworks: Standardized approaches to privacy that satisfy regulatory requirements for anti-money laundering (AML) and know-your-customer (KYC) compliance while preserving user confidentiality.
The cluster’s formation reflects a strategic decision by the Ethereum Foundation to treat privacy as a public good — infrastructure that benefits the entire ecosystem and therefore warrants coordinated funding and development, rather than being left to individual projects that may face regulatory pressure in isolation.
Key Technologies the Cluster Is Deploying
The Privacy Cluster’s work draws on several cryptographic technologies that have matured significantly over the past few years. Each addresses a different aspect of the privacy problem.
Zero-Knowledge Proofs
Zero-knowledge proofs (ZKPs) are the cornerstone of Ethereum’s privacy strategy. A ZKP allows one party to prove to another that a statement is true without revealing any information beyond the validity of the statement itself. In the context of blockchain privacy, this means a user can prove they have sufficient funds to make a payment, that they are an authorized participant in a protocol, or that a computation was performed correctly — all without revealing the underlying data.
The Privacy Cluster is working with two primary ZKP systems: zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) and zk-STARKs (Zero-Knowledge Scalable Transparent Arguments of Knowledge). SNARKs offer smaller proof sizes and faster verification, making them ideal for on-chain use where gas costs matter. STARKs avoid the need for a trusted setup ceremony and are quantum-resistant, making them attractive for long-term infrastructure.
Practical applications being developed include private token transfers where the sender, receiver, and amount are all hidden from public view; private voting mechanisms for DAO governance; and confidential DeFi positions where a user’s collateral and debt ratios are verified without being publicly exposed.
Stealth Addresses
Stealth addresses solve the problem of recipient privacy. Under the current system, if someone publishes their Ethereum address to receive payments — a freelancer invoicing a client, a charity accepting donations, a business receiving vendor payments — every subsequent transaction to that address is publicly linked. Stealth addresses allow a sender to generate a one-time address for each transaction that only the intended recipient can detect and spend from.
The mechanism works through elliptic curve cryptography. The recipient publishes a stealth meta-address. The sender uses this meta-address combined with a random value to derive a unique one-time address. The recipient scans the blockchain using their private key to identify which stealth addresses belong to them. To outside observers, there is no visible link between the stealth meta-address and the one-time addresses.
Ethereum co-founder Vitalik Buterin has been a vocal advocate of stealth addresses, and EIP-5564 (the Stealth Address standard) is a key focus of the Privacy Cluster’s application-layer workstream. Wallet providers are beginning to integrate stealth address support, with several major wallets expected to offer the feature by late 2026.
Private Mempools
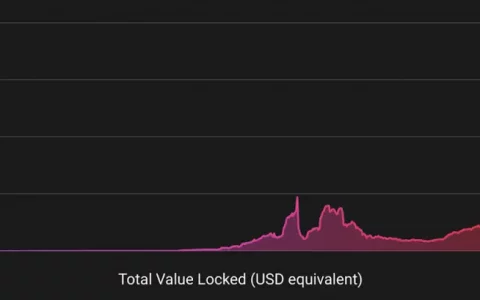
The public mempool is one of the most significant privacy vulnerabilities on Ethereum. When a user submits a transaction, it is broadcast to the network’s mempool, where it sits waiting to be included in a block. During this window, anyone can observe the transaction’s details, including the sender, receiver, amount, and the smart contract function being called. This visibility enables MEV extraction — front-running, back-running, and sandwich attacks that cost Ethereum users an estimated $1.2 billion in 2025 alone.
Private mempools, also known as encrypted mempools or shielded transaction pools, encrypt transactions before they enter the mempool. Block builders can include transactions in blocks without seeing their contents until the block is finalized. Several implementations are being explored, including threshold encryption schemes where a committee of validators collectively holds the decryption key, and fully homomorphic encryption (FHE) approaches where computations can be performed on encrypted data.
The Privacy Cluster is collaborating with Flashbots and other MEV-focused research groups to develop standardized encrypted mempool protocols that can be integrated into Ethereum’s proposer-builder separation (PBS) architecture.
Zcash and the Privacy-First Approach
While Ethereum is adding privacy after the fact, Zcash was built for it from the start. Launched in 2016, Zcash pioneered the use of zk-SNARKs for fully private cryptocurrency transactions. Its shielded pool allows users to send and receive ZEC with complete confidentiality: the sender, receiver, and amount are all encrypted on-chain.
In 2026, Zcash is experiencing a resurgence of interest driven by several developments. The Zcash community has adopted a new governance structure that decentralizes control away from the Electric Coin Company and toward a broader set of stakeholders. Technical upgrades have improved shielded transaction throughput and reduced proving times, making private transactions more practical for everyday use. And growing regulatory clarity around compliant privacy — where users can demonstrate the legitimacy of their funds without revealing the details of every transaction — has reduced the stigma that previously surrounded privacy coins.
Zcash’s approach to privacy remains fundamentally different from Ethereum’s. Zcash’s privacy is protocol-native: the shielded pool is a core feature of the blockchain, optimized and audited as part of the consensus layer. Ethereum’s privacy, even with the Privacy Cluster’s work, will rely on application-layer solutions built on top of a transparent base layer. This architectural difference has trade-offs. Zcash’s native privacy is stronger and more difficult to compromise, but Ethereum’s programmable privacy can be more flexible and can integrate with the vast DeFi ecosystem that already exists on the network.
Canton and Compliant Privacy for Enterprises
Canton Network represents a different philosophy entirely. Built by Digital Asset and backed by major financial institutions including Goldman Sachs, BNY Mellon, and Deutsche Boerse, Canton is designed for enterprises that need blockchain privacy with full regulatory compliance. Unlike public blockchains where privacy is an add-on, Canton’s architecture ensures that transaction data is only visible to the parties involved in a transaction and their designated regulators.
Canton is gaining traction in 2026 as traditional financial institutions accelerate their adoption of blockchain technology for settlement, trade finance, and asset tokenization. The network’s privacy model — where data is compartmentalized by default and regulators can be granted selective access — aligns naturally with existing financial regulations like GDPR, MiFID II, and US banking privacy laws.
For the broader crypto ecosystem, Canton’s growth highlights an important point: privacy is not a single problem with a single solution. Different users have different privacy requirements, and the market is segmenting accordingly. Retail users on Ethereum may want privacy from public observers while maintaining the ability to interact with permissionless DeFi. Institutional users on Canton need privacy from competitors while maintaining full transparency to regulators. Both needs are legitimate, and the technology is evolving to serve both.
Compliant Privacy vs. Full Anonymity
The most contentious debate in blockchain privacy is not whether privacy is desirable — nearly everyone agrees that it is — but how much privacy is acceptable in a world where governments mandate financial surveillance for anti-money laundering purposes.
Full anonymity, as exemplified by privacy coins like Monero, makes it technically impossible for anyone — including law enforcement — to trace the flow of funds. This approach maximizes individual privacy but has led to delistings from regulated exchanges and outright bans in several jurisdictions.
Compliant privacy, the model that the Ethereum Privacy Cluster and projects like Zcash are increasingly embracing, takes a middle path. The idea is to hide transaction details from the general public while preserving the ability for users to voluntarily disclose information to regulators, auditors, or counterparties when required. Technically, this is implemented through mechanisms like view keys (which allow a designated third party to see a user’s transaction history), selective disclosure proofs (which allow a user to prove specific facts about their transactions without revealing everything), and compliance oracles (on-chain services that verify a user’s regulatory status without exposing their identity).
The Privacy Cluster has explicitly adopted compliant privacy as its design philosophy. The group’s public roadmap states that privacy solutions should “protect users from mass surveillance and commercial exploitation while preserving the ability for legitimate oversight through voluntary disclosure mechanisms.” This positions Ethereum’s privacy infrastructure as compatible with existing regulatory frameworks rather than adversarial to them — a critical distinction for a network that serves institutional users and is subject to increasing regulatory scrutiny.
Blockchain Privacy Comparison Table
| Feature | Ethereum (with Privacy Cluster) | Zcash | Monero | Canton Network |
|---|---|---|---|---|
| Privacy Model | Application-layer (ZKPs, stealth addresses) | Protocol-native (shielded pool) | Protocol-native (Ring signatures, stealth addresses) | Architecture-native (data compartmentalization) |
| Default Privacy | Opt-in (transparent by default) | Opt-in (transparent and shielded pools) | Always-on (all transactions private) | Always-on (private between parties) |
| Regulatory Compliance | View keys and selective disclosure | View keys available | No built-in compliance tools | Full regulator access by design |
| Smart Contract Support | Full programmability | Limited (Zcash Shielded Assets) | No smart contracts | Daml smart contracts |
| DeFi Ecosystem | Largest in crypto | Minimal | Minimal | Enterprise-focused |
| MEV Protection | Private mempools (in development) | Not applicable (no public mempool for shielded) | Not applicable | Not applicable (permissioned network) |
| Exchange Support | Universal | Declining (delisted in some regions) | Significantly restricted | Institutional only |
| Target Users | Retail, institutional, developers | Privacy-conscious individuals | Maximum privacy advocates | Banks, enterprises, regulated entities |
The Road Ahead for Ethereum Privacy
The Privacy Cluster’s work is ambitious, but it faces significant challenges. Technical hurdles remain: zero-knowledge proof generation is still computationally expensive for complex operations, stealth address scanning requires additional infrastructure that wallets must support, and private mempools introduce new trust assumptions that must be carefully managed.
Regulatory risk is equally significant. The Tornado Cash precedent demonstrated that US authorities are willing to sanction privacy protocols, and the legal landscape around blockchain privacy remains unsettled. The Privacy Cluster’s emphasis on compliant privacy is a deliberate strategy to avoid a repeat of the Tornado Cash situation, but there is no guarantee that regulators will draw the line where Ethereum developers hope they will.
Despite these challenges, the direction of travel is clear. Privacy is moving from the margins of the Ethereum ecosystem to its center. The Foundation’s decision to fund a dedicated 47-person team signals that privacy is now treated as core infrastructure, on par with scaling, security, and decentralization. If the Privacy Cluster delivers on its roadmap, Ethereum users could have access to stealth addresses in their wallets, private token transfers through ZKP-powered protocols, and MEV-resistant transaction submission through encrypted mempools — all within the next 12 to 18 months.
The broader implication is that blockchain privacy is no longer a fringe concern associated with illicit activity. It is a mainstream infrastructure requirement driven by the same forces that made HTTPS the default for web traffic and end-to-end encryption the standard for messaging apps. The question is no longer whether crypto transactions should be private, but how to implement privacy in a way that protects individuals without enabling abuse. The Ethereum Foundation’s Privacy Cluster is the most significant attempt yet to answer that question.
Frequently Asked Questions
What is the Ethereum Foundation’s Privacy Cluster?
The Privacy Cluster is a 47-person working group created by the Ethereum Foundation to design and deploy privacy infrastructure across the Ethereum ecosystem. It includes researchers, cryptographers, protocol engineers, and policy experts organized into workstreams covering protocol-layer privacy, application tooling, network-layer privacy, and compliance frameworks.
Are private Ethereum transactions legal?
Private transactions themselves are not illegal in most jurisdictions. However, the tools used to achieve privacy may face regulatory scrutiny. The Privacy Cluster is specifically designing compliant privacy solutions that allow users to voluntarily disclose transaction information to regulators when required, distinguishing its approach from tools that offer full anonymity with no compliance mechanism.
How do stealth addresses work on Ethereum?
Stealth addresses allow a sender to generate a unique one-time address for each transaction using the recipient’s published stealth meta-address. Only the recipient can detect and access funds sent to these addresses. This breaks the public link between a recipient’s known identity and their incoming transactions. The standard is defined in EIP-5564.
What are zero-knowledge proofs in crypto?
Zero-knowledge proofs are cryptographic techniques that allow one party to prove a statement is true without revealing any underlying data. In crypto, they enable private transactions where a user can prove they have sufficient funds or meet specific criteria without exposing their balance, transaction history, or identity.
Is Zcash better than Ethereum for privacy?
Zcash offers stronger native privacy because its shielded pool is built into the protocol layer. However, Ethereum offers a far richer ecosystem of DeFi applications, smart contracts, and developer tooling. Ethereum’s privacy solutions, while application-layer add-ons rather than protocol-native features, benefit from this broader ecosystem. The best choice depends on whether a user prioritizes maximum privacy strength or access to the broader Ethereum application ecosystem.
Will Ethereum privacy features affect gas costs?
Yes, privacy features generally increase gas costs because zero-knowledge proof verification and encrypted state management require additional computation. However, advances in proof systems and Ethereum’s Layer 2 scaling solutions are reducing these costs significantly. The Privacy Cluster is working to ensure that privacy features are economically practical for everyday transactions.
Written by BTCover Editorial Team
内容搜集自网络,整理者:BTCover,如若侵权请联系站长,会尽快删除。