The cryptocurrency market in 2026 holds more value than ever before. Bitcoin trades near six figures, decentralized finance protocols manage hundreds of billions in total value locked, and real-world asset tokenization is bringing trillions of dollars worth of traditional assets on-chain. With this growth comes an uncomfortable truth: cybercriminals are more sophisticated, more motivated, and more creative than at any point in the history of digital assets. In 2025 alone, wallet exploits, phishing campaigns, and social engineering attacks drained an estimated $3.8 billion from individual holders and protocols combined.
The good news is that the vast majority of crypto theft is preventable. Unlike traditional bank accounts where fraud protection and insurance cushion the blow, cryptocurrency transactions are irreversible. Once your funds leave your wallet, they are gone. That finality makes crypto wallet security not just a best practice but an absolute necessity for anyone holding digital assets in 2026.
This guide covers everything you need to protect cryptocurrency holdings — from choosing the right wallet type to defending against modern attack vectors, securing your seed phrase, setting up proper two-factor authentication, managing DeFi token approvals, and building an emergency response plan if the worst happens.
Understanding Wallet Types and Their Security Trade-offs
Before diving into specific threats and defenses, it is essential to understand the different categories of crypto wallets available in 2026 and the security characteristics of each. Your choice of wallet is the single most consequential security decision you will make.
Hardware Wallets (Cold Storage)
Hardware wallets — such as the Ledger Stax, Trezor Safe 5, and Keystone 4 Pro — store your private keys on a dedicated, air-gapped device that never exposes those keys to the internet. When you sign a transaction, the signing happens inside the secure element of the hardware device itself. Even if the computer you connect the hardware wallet to is compromised by malware, the attacker cannot extract your private keys because they never leave the device.
Hardware wallets are the gold standard for crypto wallet security when holding significant amounts of cryptocurrency. They are not immune to all attacks — supply chain tampering and sophisticated firmware exploits have been demonstrated in research settings — but they eliminate the most common and damaging threat vectors entirely.
Software Wallets (Hot Wallets)
Software wallets like MetaMask, Phantom, Rabby, and Trust Wallet run as browser extensions or mobile applications. They store your private keys in encrypted form on your device — your laptop, phone, or tablet. This makes them convenient for frequent transactions and DeFi interactions, but it also means your keys are only as secure as the device they live on.
If your computer is infected with a keylogger or clipboard-hijacking malware, a software wallet can be emptied in seconds. Hot wallets are appropriate for funds you actively trade or use in DeFi, but they should never hold the bulk of your long-term savings.
Multi-Signature Wallets
Multi-signature (multisig) wallets require more than one private key to authorize a transaction. A common configuration is 2-of-3, meaning three keys exist and any two must sign to move funds. Gnosis Safe (now Safe) remains the leading multisig solution on Ethereum and EVM-compatible chains. Multisig wallets are ideal for teams, DAOs, and individuals who want to eliminate single points of failure. Even if one key is compromised, the attacker cannot move funds without obtaining a second key.
Smart Account Wallets (Account Abstraction)
The newest category in 2026 is smart account wallets that leverage ERC-4337 account abstraction. Wallets like Soul Wallet, Ambire, and the latest version of Argent allow users to set spending limits, define social recovery guardians, require time-delayed transactions above certain thresholds, and even whitelist destination addresses. These programmable security features represent the future of self-custody, though the technology is still maturing and smart contract risk remains a consideration.
Common Attack Vectors in 2026
Understanding how attackers steal crypto is the first step toward not becoming a victim. Here are the most prevalent and dangerous attack methods targeting crypto holders today.
Phishing Attacks
Phishing remains the single most effective attack vector in crypto. Modern phishing campaigns in 2026 are remarkably sophisticated. Attackers create pixel-perfect clones of popular DeFi platforms, NFT marketplaces, and exchange login pages. They distribute links through compromised Discord servers, fake X (Twitter) accounts, Google Ads that appear above legitimate search results, and even targeted emails that reference your actual on-chain activity.
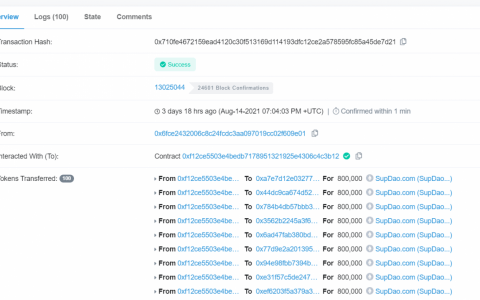
The most dangerous variant is approval phishing, where a malicious website prompts you to sign a token approval transaction that grants the attacker unlimited permission to spend your tokens. You think you are interacting with a legitimate protocol, but you are actually handing the keys to your token balances to a thief. According to blockchain analytics firm Chainalysis, approval phishing accounted for over $1.1 billion in losses in 2025.
SIM Swap Attacks
A SIM swap attack occurs when a criminal convinces your mobile carrier to transfer your phone number to a SIM card they control. Once they have your number, they can intercept SMS-based two-factor authentication codes, reset passwords on exchange accounts, and bypass phone-based verification. SIM swap attacks have been responsible for some of the largest individual crypto thefts in history, with single victims losing millions of dollars.
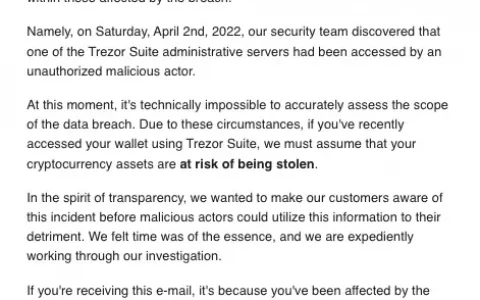
In 2026, SIM swap attacks remain a serious threat despite FCC regulations enacted in 2024 that require carriers to implement stronger identity verification. Social engineering of carrier customer service representatives continues to be effective, particularly outside the United States where regulatory protections vary.
Malware and Clipboard Hijackers
Crypto-specific malware has evolved significantly. Modern variants include clipboard hijackers that monitor your system clipboard for cryptocurrency addresses and silently replace the address you copied with the attacker’s address. When you paste what you think is your intended destination address, you are actually sending funds to the thief. Other malware families target browser extension wallets directly, extracting encrypted vault files and attempting to brute-force weak passwords offline.
In 2026, AI-generated malware distributed through fake software updates, pirated applications, and malicious npm packages has become particularly concerning. Always verify wallet addresses character by character before confirming any transaction.
Social Engineering
Social engineering attacks exploit human psychology rather than technical vulnerabilities. Common tactics include impersonating customer support agents in Telegram or Discord groups, posing as well-known crypto influencers offering exclusive investment opportunities, creating urgency through fake security alerts that claim your wallet has been compromised, and using deepfake video calls to impersonate trusted contacts. The rise of generative AI has made these impersonation attacks dramatically more convincing and harder to detect.
Seed Phrase Security: The Foundation of Everything
Your seed phrase (also called a recovery phrase or mnemonic) is the master key to your cryptocurrency. It is typically a sequence of 12 or 24 words generated when you create a new wallet. Anyone who possesses these words in the correct order can reconstruct your private keys and drain every asset in your wallet from any device, anywhere in the world. Protecting your seed phrase is the single most important aspect of crypto security best practices.
Rules for Seed Phrase Protection
- Never store your seed phrase digitally. Do not type it into a note-taking app, save it in a text file, email it to yourself, photograph it, store it in cloud storage, or enter it into any website — ever. Digital storage creates attack surfaces that are impossible to fully control.
- Write it on durable, physical media. Paper works for short-term storage, but it is vulnerable to fire, water, and degradation. For long-term holdings, invest in a steel seed phrase backup plate (such as Cryptosteel, Billfodl, or Blockplate). These withstand fire, flooding, and physical damage that would destroy paper.
- Store copies in geographically separated, secure locations. A fireproof safe at home and a bank safety deposit box in another location is a common approach. The goal is to ensure that no single disaster — fire, flood, theft, or natural catastrophe — can destroy all copies of your seed phrase.
- Consider splitting your seed phrase. Advanced users can split a 24-word seed phrase into multiple parts using Shamir’s Secret Sharing (SSS), which allows you to reconstruct the full phrase from a subset of the parts. For example, you could create five shares and require any three to reconstruct the seed. Trezor’s hardware wallets natively support Shamir backup.
- Never share your seed phrase with anyone. No legitimate company, protocol, customer support agent, or wallet provider will ever ask for your seed phrase. Any request for your seed phrase is a scam — no exceptions.
Two-Factor Authentication Best Practices
Two-factor authentication (2FA) adds a second layer of verification beyond your password when logging into exchanges, email accounts, and other services connected to your crypto holdings. However, not all 2FA methods are created equal, and choosing the wrong one can create a false sense of security.
The 2FA Hierarchy (Best to Worst)
- Hardware security keys (YubiKey, Google Titan): Physical devices that use the FIDO2/WebAuthn standard. They are phishing-resistant because the key cryptographically verifies the domain of the website requesting authentication. Even if you land on a phishing site, the key will refuse to authenticate. This is the best 2FA method available.
- Authenticator apps (Google Authenticator, Authy, Aegis): These generate time-based one-time passwords (TOTP) that change every 30 seconds. They are significantly more secure than SMS because the codes are generated locally on your device and cannot be intercepted through a SIM swap. Always back up your 2FA recovery codes securely.
- SMS-based 2FA: The weakest form of 2FA and actively dangerous for crypto holders. SMS codes can be intercepted via SIM swap attacks, SS7 protocol vulnerabilities, and social engineering of carrier employees. If you are still using SMS-based 2FA on any account connected to crypto, switch to an authenticator app or hardware key immediately.
Apply 2FA to every account in your security chain, not just your exchange accounts. This includes your email (the most critical — a compromised email enables password resets everywhere), your cloud storage, your phone carrier account, and any social media accounts connected to your crypto identity.
Setting Up a Hardware Wallet Correctly
Buying a hardware wallet is not enough. How you set it up and use it determines whether it actually protects your assets. Follow these steps for a secure hardware wallet setup in 2026.
- Buy directly from the manufacturer. Never purchase a hardware wallet from Amazon third-party sellers, eBay, or any unofficial reseller. Supply chain attacks — where a device is tampered with before you receive it — are a real and documented threat. Order directly from Ledger, Trezor, or Keystone’s official websites.
- Verify the device is sealed and untampered. Check tamper-evident packaging. If the device arrives with signs of opening or if the holographic seal is broken, do not use it. Contact the manufacturer for a replacement.
- Initialize the device in a private, secure environment. Set up your wallet at home, not in a coffee shop or coworking space. Ensure no cameras are pointed at your screen or the device during seed phrase generation.
- Write down your seed phrase on physical media immediately. Follow the seed phrase security guidelines above. Double-check every word. Many wallets will quiz you on the words during setup — take this step seriously.
- Set a strong PIN. Choose a PIN that is at least 6 digits and not based on personal information like birthdays or anniversaries. The PIN protects the device if it is physically stolen.
- Enable a passphrase (optional but recommended for advanced users). A passphrase acts as a “25th word” added to your seed phrase, creating an entirely separate set of accounts. This provides plausible deniability and an additional layer of security. If someone forces you to unlock your wallet, the passphrase-protected accounts remain hidden.
- Test with a small transaction first. Before transferring your main holdings, send a small amount to the hardware wallet and verify that you can sign a transaction and send it back. This confirms that the setup is working correctly.
- Keep firmware updated. Hardware wallet manufacturers regularly release firmware updates that patch vulnerabilities and add features. Always update through the official companion app (Ledger Live, Trezor Suite) and verify the update’s authenticity.
DeFi Approval Risks and How to Revoke Token Approvals
Every time you interact with a DeFi protocol — swapping tokens on Uniswap, depositing into a lending pool on Aave, or minting an NFT — you typically grant that protocol’s smart contract permission to spend a specific token from your wallet. These permissions, called token approvals, are one of the most overlooked and dangerous aspects of crypto wallet security.
Why Token Approvals Are Dangerous
Most DeFi protocols request unlimited token approvals by default. This means the smart contract can spend an unlimited amount of the approved token from your wallet at any time, without further permission. If the protocol’s smart contract is exploited by a hacker, or if you accidentally approved a malicious contract, the attacker can drain your entire balance of that token.
Even legitimate protocols can become attack vectors. Smart contract upgrades can introduce vulnerabilities. Protocol teams can go rogue. Admin keys can be compromised. An approval you granted to a trustworthy protocol last year might be exploited through a vulnerability discovered today.
How to Manage and Revoke Approvals
- Audit your existing approvals regularly. Use tools like Revoke.cash, Etherscan’s Token Approval Checker, or De.Fi’s Shield tool to see every active token approval associated with your wallet address. You will likely be surprised by how many unlimited approvals you have granted over time.
- Revoke approvals you no longer need. If you are no longer using a protocol, revoke its token approval. Revoking is a simple on-chain transaction that sets the approved amount to zero. It costs a small gas fee but eliminates the risk.
- Set custom approval amounts. When approving a new transaction, modify the approval amount to only the amount you intend to use, rather than accepting the unlimited default. Most wallet interfaces (MetaMask, Rabby) allow you to edit the approval amount before confirming. This limits your exposure if the contract is compromised.
- Use wallets with built-in approval management. Rabby wallet and the latest version of MetaMask include features that warn you about risky approvals and make it easy to review and revoke them directly within the wallet interface.
Operational Security Habits for Daily Use
Beyond the technical measures above, crypto security best practices require disciplined daily habits. Here are the operational security (OpSec) rules that experienced crypto holders follow.
- Use a dedicated device for crypto. Ideally, use a separate laptop or phone exclusively for crypto transactions — one that you do not use for general web browsing, downloading software, or opening email attachments. This dramatically reduces the attack surface for malware.
- Bookmark legitimate sites. Always access exchanges and DeFi protocols from bookmarks rather than searching for them. Phishing sites routinely appear in search engine ads above legitimate results.
- Verify addresses on the hardware wallet screen. When sending a transaction, always verify the destination address on the hardware wallet’s screen, not on your computer monitor. Malware can alter what you see on your computer screen while the hardware wallet shows the actual transaction details.
- Use a VPN on public networks. If you must access crypto services on public Wi-Fi, use a reputable VPN to encrypt your traffic. Better yet, avoid accessing crypto accounts on public networks entirely.
- Keep a low profile. Do not publicly disclose the size of your crypto holdings on social media. Wealthy holders are targeted for physical theft, extortion, and sophisticated social engineering. The less attackers know about your holdings, the less motivated they are to target you.
- Separate your identities. Use a dedicated email address for crypto exchange accounts that you do not use for any other purpose. This limits the impact of data breaches from other services.
Emergency Plan: What to Do If Your Wallet Is Compromised
Even with the best security practices, compromises can happen. Having an emergency plan prepared before an incident occurs can be the difference between losing some funds and losing everything.
Immediate Steps
- Transfer remaining assets immediately. If you suspect your wallet is compromised, move any remaining funds to a known-safe wallet as fast as possible. Speed is critical — attackers often use automated bots that drain wallets within minutes of gaining access.
- Revoke all token approvals. Use Revoke.cash to immediately revoke every active token approval on the compromised wallet. This prevents the attacker from draining tokens through existing approvals even if they cannot access your private key directly.
- Secure your email and exchange accounts. Change passwords and 2FA settings on all accounts associated with the compromised wallet. If you suspect a SIM swap, contact your mobile carrier immediately to lock your account and port your number back.
- Check for malware. Run a full system scan with reputable antivirus software. Consider wiping and reinstalling your operating system if you suspect your device is compromised. Do not reuse the compromised device for crypto until you are confident it is clean.
After the Incident
- Document everything. Record transaction hashes, timestamps, wallet addresses involved, and any communications with the attacker. This information is critical for law enforcement reports and potential asset recovery.
- Report to law enforcement. File reports with your local police, the FBI’s IC3 (Internet Crime Complaint Center) if you are in the US, and any relevant regulatory bodies. While recovery rates for stolen crypto remain low, reporting creates a paper trail that can help in investigations and future legal proceedings.
- Contact blockchain analytics firms. Companies like Chainalysis, TRM Labs, and Crystal Blockchain offer asset tracing services that can follow stolen funds across chains and exchanges. If the stolen funds land on a centralized exchange, there is a chance that law enforcement can freeze them.
- Create a new wallet on a clean device. Do not reuse the compromised seed phrase or any wallet derived from it. Generate a completely new seed phrase on a verified-clean hardware wallet and start fresh.
- Conduct a post-mortem. Determine how the compromise happened. Was it a phishing link? A malicious approval? A compromised device? Understanding the root cause prevents repeat incidents.
Security Checklist for 2026
Use this checklist to audit your current security posture. Every item you can check off meaningfully reduces your risk of losing funds.
| Security Measure | Priority | Status |
|---|---|---|
| Store majority of holdings in a hardware wallet | Critical | ☐ |
| Seed phrase written on steel and stored in two locations | Critical | ☐ |
| Hardware security key (YubiKey) for exchange and email 2FA | Critical | ☐ |
| No SMS-based 2FA on any crypto-related account | Critical | ☐ |
| Dedicated email for crypto accounts | High | ☐ |
| Token approvals audited and unnecessary ones revoked | High | ☐ |
| Custom (limited) approval amounts on DeFi interactions | High | ☐ |
| Hardware wallet purchased directly from manufacturer | High | ☐ |
| Dedicated device for crypto transactions | Medium | ☐ |
| VPN used on all non-private networks | Medium | ☐ |
| Emergency plan documented and tested | Medium | ☐ |
| Passphrase enabled on hardware wallet | Medium | ☐ |
Frequently Asked Questions
What is the safest type of crypto wallet in 2026?
A hardware wallet (such as Ledger Stax, Trezor Safe 5, or Keystone 4 Pro) remains the safest option for storing significant crypto holdings. For maximum security, combine a hardware wallet with a multisig setup or use account abstraction wallets with time-locked transactions and social recovery.
Can my crypto be stolen if I use a hardware wallet?
A hardware wallet protects your private keys, but it does not protect you from signing malicious transactions. If you approve a phishing transaction or grant a malicious token approval, your tokens can be stolen even though your hardware wallet is functioning correctly. Always verify transaction details on the hardware wallet screen before signing.
What should I do if I lose my seed phrase?
If you lose your seed phrase but still have access to your wallet, immediately create a new wallet with a new seed phrase and transfer all assets to the new wallet. Your old wallet is now at risk because you have lost your backup and recovery mechanism. If you have lost both the seed phrase and access to the wallet device, the funds are permanently unrecoverable.
Is it safe to store my seed phrase in a password manager?
This is a debated topic. A high-quality password manager like 1Password or Bitwarden provides strong encryption, but it still stores your seed phrase digitally, which violates the principle of keeping seed phrases offline. If your password manager is compromised through a master password breach or a vulnerability in the software, your seed phrase is exposed. For most users, physical storage on steel plates in secure locations remains the safer approach.
How often should I revoke token approvals?
Review and revoke unnecessary token approvals at least once a month if you are an active DeFi user. After interacting with any new or unfamiliar protocol, check your approvals immediately. Set a calendar reminder to perform a monthly approval audit using Revoke.cash or a similar tool.
What is the best 2FA method for crypto exchanges?
A hardware security key (YubiKey or Google Titan) using the FIDO2/WebAuthn standard is the best 2FA method. It is phishing-resistant and cannot be intercepted through SIM swap attacks. If a hardware key is not available, use an authenticator app like Google Authenticator or Aegis. Never rely solely on SMS-based 2FA for crypto accounts.
Final Thoughts
Crypto wallet security in 2026 is not about any single tool or technique. It is about building layers of defense that make it exponentially harder for an attacker to reach your assets. A hardware wallet protects your keys. Strong 2FA protects your exchange accounts. Seed phrase discipline ensures you can recover from device failure without creating digital attack surfaces. Approval management limits your exposure in DeFi. And an emergency plan ensures that even if one layer fails, you can respond quickly enough to minimize damage.
The threat landscape will continue to evolve. AI-powered phishing, deepfake social engineering, and increasingly sophisticated malware will push attackers’ capabilities forward. But the fundamentals of self-custody security — keeping keys offline, verifying before signing, and maintaining operational discipline — will remain effective regardless of how the technology changes. Invest the time to implement these crypto security best practices today, and your future self will thank you.
Written by BTCover Editorial Team. Last updated March 2026.
内容搜集自网络,整理者:BTCover,如若侵权请联系站长,会尽快删除。